Modern Automotive SPICE (ASPICE) development – particularly in software-defined vehicles and safety-critical automotive systems – faces unprecedented complexity. Today’s vehicles can contain up to approximately 100-150 million lines of code, with software driving up to 90% of future automotive innovation (including ADAS and autonomous driving systems). Managing this complexity requires robust oversight and structured documentation.
Traceability in the automotive industry, often referred to as automotive requirements traceability and lifecycle traceability, is a critical requirement embedded within key standards such as Automotive SPICE and ISO 26262 (an international standard for functional safety that governs the development of electrical, electronic, and programmable devices in the automotive industry to ensure safety throughout the life cycle of automotive products), ensuring product quality, functional safety compliance, and safety across the entire development lifecycle and supply chain.
In practice, traceability acts as the backbone connecting ASPICE process requirements with ISO 26262 functional safety objectives, enabling organizations to achieve ASPICE process compliance while maintaining rigorous safety assurance.
This piece explores best practices for building robust end-to end traceability frameworks that support both ASPICE capability levels and ISO 26262 compliance requirements in modern automotive software development.
Understanding ASPICE and ISO 26262 Traceability Requirements
What Is ASPICE Traceability
Automotive SPICE (ASPICE) is a process assessment model used to evaluate development processes for automotive systems, including electronic control units (ECUs), embedded software, and other software-intensive automotive products. Its capability dimension contains six capability levels, from Level 0 to Level 5, and provides OEMs and suppliers with a structured basis for assessing and improving process capability, software quality, and engineering discipline.
Within ASPICE, traceability (often defined as bidirectional requirements traceability) is expressed through the requirement for consistency and bidirectional traceability between key engineering artifacts across the development lifecycle. Depending on the process area, this includes links such as stakeholder requirements to system requirements, system requirements to system architecture, and system requirements to software requirements.
In practice, teams need to demonstrate a clear, auditable path from upstream requirements to downstream design, implementation, and verification artifacts (i.e., full lifecycle traceability). These links should be maintained as work products evolve, because traceability supports consistency, change impact analysis, and evidence of requirements coverage. Automotive SPICE also makes clear that traceability alone does not automatically prove consistency; the linked artifacts must also remain aligned in substance and intent.
ISO 26262 Traceability Mandates
ISO 26262 is the international standard for the automative functional safety of automotive electrical and electronic systems. It addresses hazards caused by malfunctioning behavior and defines functional safety lifecycle activities that extend from concept through development, validation, and verification.
A central concept in ISO 26262 is the Automotive Safety Integrity Level (ASIL), which classifies risk from ASIL A to ASIL D. In the concept phase, hazard analysis and risk assessment (HARA) is used to evaluate hazardous events based on severity, exposure, and controllability: a key element of risk-based safety engineering.
From a traceability perspective, ISO 26262 requires safety requirements, work products, and verification evidence to remain linked throughout the safety lifecycle (i.e., safety lifecycle traceability). This includes maintaining traceable connections between identified hazards, safety goals, derived safety requirements, and the verification and validation activities used to demonstrate that those requirements have been met. Bidirectional traceability is especially important because it supports both forward coverage and backward confirmation from tests and review evidence to originating safety requirements.
Key Differences Between ASPICE and ISO 26262 Traceability
Automotive SPICE (ASPICE) focuses on process capability and maturity assessment across software and systems development activities, while ISO 26262 concentrates on functional safety requirements, hazard mitigation, and risk reduction. Despite these different objectives, the two standards share significant overlap in their expectations for traceability and requirements lifecycle management.
In practice, organizations often adopt a unified traceability approach that supports both ASPICE process compliance and ISO 26262 safety lifecycle requirements (often called a unified compliance traceability framework). Rather than treating them separately, many teams map requirements, work products, and verification artifacts across both frameworks using integrated traceability structures or compliance matrices, enabling assessments and audits to complement each other while minimizing duplication and improving efficiency.
ASPICE assessors evaluate objective evidence that process outcomes are achieved, with traceability acting as a key mechanism for demonstrating requirement coverage, implementation traceability, and verification traceability across engineering artifacts. ISO 26262, on the other hand, relies on traceability to demonstrate that safety-critical aspects are systematically addressed, implemented, and validated throughout the safety lifecycle.
V-Model Traceability Framework
Both ASPICE and ISO 26262 are commonly implemented using a V-model development framework (a widely used systems engineering and software development lifecycle model which describes the relationship between each phase of the development life cycle and its corresponding testing phase), which structures the relationship between requirements decomposition and verification activities.
On the left side of the V-model, stakeholder requirements are refined into system and software requirements, followed by architecture and design definitions: supporting requirements decomposition and system design traceability. On the right side, integration, verification, and validation activities ensure that each level of implementation fulfills its corresponding requirements.
Within this model, three key traceability dimensions are typically established:
- Vertical traceability (or hierarchical traceability) connects artifacts across abstraction levels, from stakeholder requirements through system and software requirements down to architecture, units, and code.
- Horizontal traceability links artifacts at the same abstraction level to their corresponding verification activities, such as system requirements to system test cases.
- Bidirectional traceability enables navigation in both directions, allowing teams to trace requirements forward into implementation and tests, or backward from defects, test results, and changes to their originating requirements (critical for audit readiness and compliance evidence).
Traceability in Automotive Development
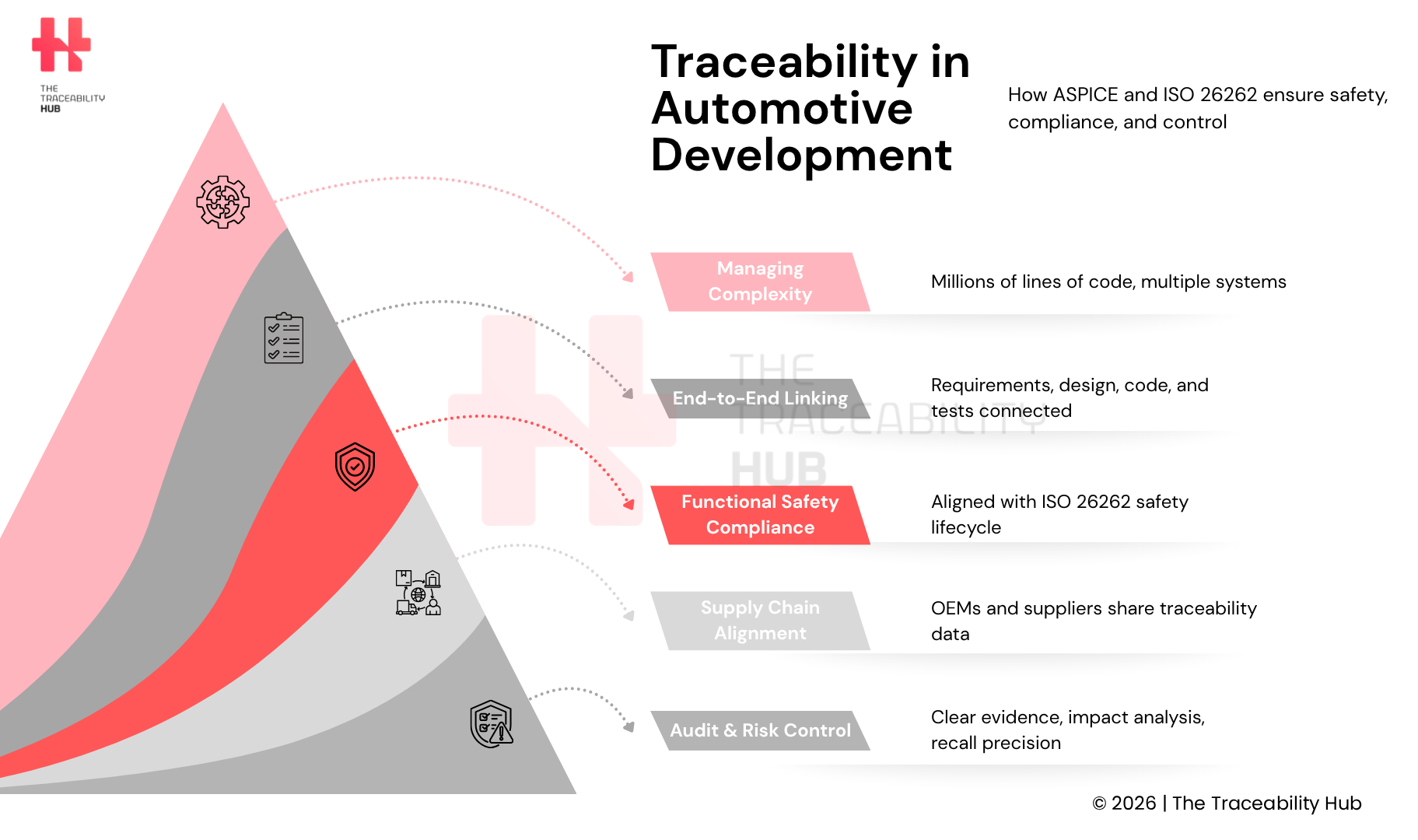
Why Traceability Is Critical in Automotive Software Development
Traceability failures in automotive software development commonly lead to broken links between requirements and tests, inconsistent deliverables, and difficulty demonstrating compliance during assessments and audits. These gaps can jeopardize compliance while generating costly rework, delayed releases, and project delays across both OEMs and Tier 1 suppliers.
Ensuring Safety Requirements Coverage
Within ISO 26262, traceability is a fundamental mechanism for managing safety requirements across the entire development lifecycle. The standard requires safety-related work products to be traceable, consistent, and properly documented from concept through implementation and verification (i.e., end-to-end safety traceability).
In practice, this means maintaining traceable relationships between hazards, safety goals, derived safety requirements, design and implementation artifacts, and the corresponding verification and validation results. Without systematic traceability management, gaps or inconsistencies in these links can make it difficult to demonstrate compliance and ensure full requirements coverage and safety validation.
Verification and validation activities rely on traceable connections between test cases, reviews, and the safety requirements they are intended to validate (i.e., test-to-requirement traceability). Manufacturers must demonstrate that safety requirements are addressed, implemented, and verified at each stage of development.
This structured approach helps ensure that safety-critical aspects receive appropriate attention according to their assigned Automotive Safety Integrity Levels (ASILs) and reduces the risk of gaps that could compromise vehicle safety and regulatory compliance.
Managing Complex Supply Chain Dependencies
Modern automotive supply chains (including multi-tier global supplier ecosystems) are highly complex, involving multiple tiers of suppliers across different countries, tools, and engineering domains. A single vehicle program may depend on dozens of suppliers, creating interdependencies that are difficult to manage without structured end-to-end automotive traceability systems.
Aligning OEM-level requirements with supplier system specifications is therefore critical for both Automotive SPICE compliance and ISO 26262 safety validation, including supplier traceability alignment and compliance mapping.
ISO 26262 (Part 2:2018) requires clear definition of roles, responsibilities, and work-product ownership across distributed development environments, including supplier relationships. In practice, this means OEMs and suppliers must align on traceability requirements, data exchange standards, and documentation practices.
This includes defining consistent templates for safety plans and requirements specifications, as well as ensuring that each party understands which work products, they are responsible for maintaining. Misalignment between OEMs and suppliers can lead to traceability gaps, broken links, data inconsistencies, and increased compliance risks.
Reducing Recall Risks and Costs
Large-scale recalls highlight the consequences of insufficient visibility across complex supply chains and lack of component-level traceability. For example, the Takata airbag recall affected tens of millions of vehicles across multiple automakers worldwide, demonstrating the risks of limited traceability and inadequate defect isolation capabilities.
More broadly, millions of vehicles are recalled each year due to quality and safety-related issues, many of which originate from component-level failures or supply chain inconsistencies. While not all issues are preventable, stronger traceability, real-time data visibility, and integrated risk management can help identify potential problems earlier in the development lifecycle.
Traceability enables manufacturers to precisely identify which components, batches, and vehicles are affected by a defect (i.e., granular product traceability and defect tracking). For example, a faulty brake sensor can be traced back to a specific production batch, linked to the assemblies in which it was installed, and ultimately to the exact vehicles impacted.
This level of precision allows manufacturers to limit recalls to targeted populations rather than entire production runs, significantly reducing costs, improving recall management efficiency, and protecting brand reputation and customer safety.
Meeting OEM and Regulatory Requirements
Traceability in the automotive industry is a critical requirement embedded within major standards and regulatory frameworks, rather than a best practice alone. Standards such as IATF 16949 require organizations to ensure product identification, traceability, and controlled production processes, supported by structured documentation and audit trails.
In practice, digital traceability systems, including automotive traceability software platforms, can support structured data collection, documentation, and reporting, helping organizations streamline audit preparation and demonstrate compliance more efficiently.
OEMs such as BMW, Mercedes-Benz and Volkswagen typically require high levels of traceability across their supply chains (including supplier traceability compliance and data transparency). Suppliers are expected to provide timely, accurate, and consistent data linking requirements, components, and production processes.
Compliance with global safety and quality standards relies on demonstrable traceability that shows how requirements have been addressed, implemented, and verified throughout the development and production lifecycle.
Building End-to-End Traceability in ASPICE Projects
The Automotive SPICE framework defines specific base practices across engineering processes that establish traceability between development artifacts. Organizations are expected to demonstrate traceability across key lifecycle work products, from stakeholder requirements through design, implementation, and verification, supporting complete requirements lifecycle traceability.
Requirements to Design Traceability
ASPICE expects clear, bidirectional traceability between requirements and architectural or design elements (i.e., requirements-to-architecture traceability). System requirements should be linked to architecture decisions that address them, while software requirements are connected to the design elements that realize their functionality.
In many organizations, this traceability is supported using requirements management and lifecycle tools such as IBM DOORS Next or Siemens Polarion (widely used ALM and requirements traceability tools). These tools enable the use of unique requirement identifiers and traceability views that help visualize coverage across requirements, design, and verification artifacts.
Where model-based development (MBSE) is used, architecture or model elements (e.g., UML or SysML diagrams) can be linked to requirements through identifiers or metadata. This creates navigable connections between textual requirements and design representations, supporting impact analysis, consistency validation, and helping reduce gaps or inconsistencies.
Design to Implementation Traceability Links
ASPICE also requires traceability between software requirements and implementation artifacts (i.e., design-to-code traceability). Software units should be traceable back to the requirements they implement, creating verifiable connections between specifications and code.
In practice, this is often achieved through structured naming conventions, metadata, and references within development tools, rather than relying solely on code comments. A single requirement may map to one or more implementation elements, depending on system complexity and software architecture design.
Maintaining these links throughout development helps ensure that all implemented functionality is justified by a requirement, reducing the risk of orphaned code and supporting verification, validation, and compliance audit activities.
Implementation to Test Case Traceability
Test specifications are expected to reference requirement identifiers or maintain clear links to the requirements they verify. This establishes transparent verification paths for each functional element and supports test coverage analysis.
The Automotive SPICE framework requires traceability between software requirements and corresponding test cases, enabling organizations to demonstrate coverage of requirements through verification activities. Test management systems often provide coverage views or traceability matrices that show which requirements are linked to test cases, and which may lack sufficient verification (supporting gap analysis and audit readiness).
In more mature environments, automated test scripts can include requirement annotations, and traceability tools can track execution results against originating requirements. This helps teams demonstrate that testing activities are aligned with defined requirements and support both ASPICE compliance and broader quality software assurance objectives.
Bidirectional Traceability Between Artifacts
ASPICE emphasizes bidirectional traceability across engineering artifacts; a cornerstone of automotive requirements traceability best practices. This allows teams to navigate from requirements forward to design, implementation, and tests, or backward from defects, test results, and changes to the originating requirements.
This dual-direction capability supports change impact, defect traceability, and compliance verification, helping ensure that development artifacts remain aligned with valid requirements. Forward traceability tracks how requirements are realized across development stages, while backward traceability helps confirm that implemented elements are justified by documented requirements, reducing the risk of unnecessary or undocumented functionality.
Change Effect Analysis Through Traceability
Traceability enables systematic assessment of proposed changes by identifying affected artifacts across the development lifecycle (i.e., traceability-driven impact analysis). Traceability tools and structured linkages can support automated or semi-automated impact analysis, highlighting which design elements, code modules, and test cases may require updates when requirements evolve.
This allows teams to better assess risks, effort, and downstream consequences before implementing changes. By making dependencies visible, traceability reduces the risk of human error in change management and supports more informed data-driven decision-making throughout the automotive development lifecycle.
ISO 26262 Compliance Through Traceability Management
The ISO 26262 framework defines a functional safety lifecycle and associated requirements for automotive electrical and electronic systems, while allowing tailoring of activities based on system context and risk (i.e., risk-based safety lifecycle management).
The standard defines four Automotive Safety Integrity Levels (ASILs), from ASIL A (lowest risk reduction) to ASIL D (highest risk reduction), with requirements that scale in rigor according to the assigned ASIL.
ASIL-Based Traceability Requirements
ASIL classification influences the level of rigor applied to development, verification, validation, and supporting traceability practices throughout the lifecycle. ASIL is determined during hazard analysis and risk assessment (HARA) based on severity, exposure, and controllability of potential hazardous events.
Higher ASIL ratings require more rigorous engineering processes, including more comprehensive documentation, verification, and validation activities (i.e., high-integrity safety engineering practices). While ISO 26262 does not prescribe specific traceability structures, maintaining consistent and well-structured traceability becomes essential to demonstrate coverage of safety requirements across development and verification activities.
For higher ASIL levels (e.g., ASIL D), verification and validation activities are more extensive and may include advanced techniques such as fault injections or robustness testing, depending on system context. Traceability supports these activities by linking safety requirements to implementation and verification evidence across the lifecycle (i.e., safety-critical traceability links).
Safety Goal to Functional Safety Requirement Traceability
Safety goals represent top-level safety objectives derived from hazard analysis and are intended to prevent or mitigate unreasonable risk associated with hazardous events. Each safety goal is assigned an ASIL and defines the basis for deriving functional safety requirements (i.e., top-down safety requirements decomposition).
Functional safety requirements are then refined into system-level requirements and further allocated to hardware and software components. Throughout this process, traceability should be maintained between safety goals, derived requirements, design elements, and verification specifications (i.e., hierarchical safety traceability structure).
This hierarchical traceability structure supports consistency, enables impact analysis, and helps demonstrate that safety requirements are properly implemented and verified at each level of the system architecture.
Hazard Analysis and Risk Assessment (HARA) Traceability
HARA is a core ISO 26262 activity used to identify and assess hazardous events in automotive electrical and electronic systems. In this process, hazardous events are evaluated using three factors: severity, exposure, and controllability. The results of HARA are used to derive safety goals and assign ASILs, with traceability then maintained from hazards to safety goals, functional safety requirements, and downstream system, hardware, and software requirements.
Verification and Validation Traceability
ISO 26262 requires documented verification and validation activities across the safety lifecycle, along with traceable links between safety requirements, verification specifications, and results (i.e., verification traceability and validation traceability).
Hardware and software safety requirements should be bidirectionally traceable to the tests, reviews, analyses, or other verification methods used to demonstrate compliance. In practice, many organizations manage these artifacts in version-controlled tools with change tracking, but that is an implementation choice rather than wording I could verify as a direct ISO requirement from the publicly accessible sources. Advanced methods such as constrained-random testing, assertions, and coverage can also be applied to strengthen verification coverage and safety assurance.
Documentation and Audit Trail Requirements
For assessment and audit readiness, organizations need a clear chain of evidence linking safety requirements to design, implementation, verification, and release decisions (i.e., compliance audit trail and traceability documentation).
ISO 26262 Part 8 includes confirmation measures such as confirmation reviews and functional safety audits to assess the adequacy and completeness of safety-related work products. Robust configuration and change management support this audit trail, even where the exact toolchain varies from one organization to another.
Tools and Best Practices for Automotive Traceability
Appropriate tooling plays a critical role in enabling scalable and sustainable traceability in ASPICE-based automotive projects. Without structured tool support, maintaining traceability across complex development lifecycles can become a significant manual burden and increase the risk of inconsistencies or compliance gaps.
ALM and Requirements Management Tools
Application Lifecycle Management (ALM) platforms support traceability across the development lifecycle, from initial requirements through design, implementation, testing, release, and ongoing updates (i.e., end-to-end lifecycle traceability management).
Tools such as IBM DOORS Next, Siemens Polarion, and Perforce ALM enable teams to manage requirements, maintain traceability links, analyze change impacts, and monitor coverage across development artifacts, widely recognized automotive traceability tools and ALM platforms.
These platforms can generate traceability matrices and coverage views based on established links, helping teams identify gaps and inconsistencies while reducing manual documentation effort. However, effective traceability still depends on well-defined processes, consistent data management, and disciplined use of tools.
Automated Traceability Matrix Generation
Automation can further support traceability by helping maintain and visualize relationships between requirements, design elements, code, and test artifacts (i.e., automated traceability mapping and reporting). Some modern tools and AI-assisted approaches can suggest or support the creation of traceability links and dynamically update traceability views as artifacts evolve.
Rather than eliminating manual effort entirely, these systems reduce the burden of maintaining traceability and help ensure that changes in requirements, tests, or design elements are identified and managed consistently. Many tools also flag impacted or potentially inconsistent links, supporting impact analysis and compliance reporting.
Configuration Management and Version Control
Version control systems track changes to code and other development artifacts over time, supporting traceability of changes and configuration history. Tools such as Git maintain a detailed history of detailed change, including information about authors, timestamps, and commit messages.
Configuration management complements version control by establishing baselines, controlling changes, and maintaining visibility over system configurations (i.e., configuration traceability and baseline management). It ensures that teams can identify what has changed, when, and by whom, while supporting controlled releases and audits.
While version control systems such as Git enable rollback to previous states, effective configuration management typically involves a broader set of processes and tools to manage system-level consistency across the development lifecycle.
Supplier Collaboration and Traceability
Complex automotive supply chains require continuous coordination across multiple tools, domains, and organizations. Engineering teams often work with combinations of MBSE, ALM, and PLM tools that do not natively interoperate, making it challenging to maintain consistent traceability links (i.e., cross-tool traceability integration challenges).
Suppliers frequently use different tool chains than OEMs. For example, some may rely on IBM DOORS Next, others on Siemens Polarion, while smaller organizations may still depend on spreadsheets or custom systems.
To address this fragmentation, integration and link management platforms can enable federated traceability across heterogeneous environments, allowing organizations to exchange and maintain traceability data without requiring a single unified tool chain.
Common Traceability Implementation Challenges
Implementing traceability in complex automotive environments presents a range of practical challenges. Manual recordkeeping can introduce errors and inconsistencies, while fragmented toolchains often create data silos that break traceability gaps across systems.
Without proper integration and governance, these issues can lead to incomplete traceability, reduced visibility, and increased effort during audits and compliance assessments. Addressing these challenges typically requires a combination of process standardization, tool integration, and disciplined data governance and traceability management practices.
Building Scalable Traceability for ASPICE and ISO 26262
Effective traceability frameworks support both ASPICE process capability objectives and ISO 26262 functional safety requirements in modern automotive development (i.e., scalable automotive traceability frameworks). Organizations are expected to establish bidirectional traceability across key lifecycle artifacts, connecting requirements, design, implementation, and verification activities within a structured development model such as the V-model.
Application Lifecycle Management (ALM) tools can significantly reduce manual documentation effort by supporting the creation and maintenance of traceability links, as well as generating up-to-date traceability and coverage views. These capabilities help organizations support compliance with OEM expectations and applicable safety and quality standards.
Combined with version control, configuration management, and federated integration platforms, traceability enables more effective collaboration across complex supplier networks and heterogeneous toolchains.
Organizations that implement these practices can improve visibility across the development lifecycle, help reduce recall risks, and strengthen audit readiness. In doing so, they are better positioned to demonstrate that safety requirements have been systematically addressed, implemented, and verified – ensuring both ASPICE compliance and ISO 26262 certification readiness.
Read more: RFID Traceability for Automotive Chemicals: Gaining Control Over Third-Party Shipping