Why Integration Matters in Tax Stamps and Track & Trace
As excise control system, illicit-trade prevention system and supply-chain transparency initiatives gain importance, tax stamps and secure track & trace systems (also referred to as track and trace solutions or supply chain traceability systems) are receiving growing attention from governments and industry alike. Yet in many markets, the discussion is still fragmented: some stakeholders focus primarily on tax collection and excise revenue protection, others on anti-counterfeiting measures and product authentication, while others still treat tax stamps mainly as physical proof of tax payment or compliance labels. ISO 22382:2018, for example, frames excise tax stamps more broadly, as part of a system covering security features, issuance processes and examination protocols.
In practice, tax stamps, authentication technologies and traceability systems are often most effective when designed as part of an integrated excise control and revenue protection framework. Used together, they can help governments improve excise oversight, support audits and enforcement, strengthen legal supply chains and reduce tax leakage and illicit trade risks. In tobacco, this approach is reflected in the WHO Protocol to Eliminate Illicit Trade in Tobacco Products, whose Article 8 requires tracking and tracing systems and unique identification markings. WHO (World Health Organization) also notes that illicit trade can be addressed while increasing tobacco taxes, with gains in revenue and reductions in tobacco use.
The case for integration is also practical and evidence based. The World Bank notes that illicit tobacco trade causes substantial annual tax revenue losses globally and that excise tax stamps and track & trace systems can facilitate tax collection, audits, compliance monitoring, and enforcement actions across distribution. More broadly, the OECD reports that counterfeit goods infiltrating supply chains deprive governments of revenue and create public-health and safety risks, reinforcing the need for secure authentication and traceability solutions.
For that reason, many governments and market participants are paying closer attention not only to track & trace technology solutions, but also to standards, governance models and implementation capabilities. In this context, solution providers with experience in highly regulated industries (such as pharmaceuticals, tobacco, and alcohol) can play a useful role by supporting public authorities and industry with technology, training and implementation guidance. ITSA itself describes part of its mission as improving understanding of the benefits of tax-stamp programs and promoting professional standards and best practices in the sector.
A simple way to frame the issue is this: when traceability systems and authentication technologies are combined effectively, they can contribute to stronger supply chain security, better enforcement and more reliable revenue protection.
What Is a Tax Stamp?
A tax stamp (or excise stamp) is a visible stamp, label or secure mark placed on consumer goods to indicate that applicable excise duties or indirect taxes have been paid or are due to be paid. At its most basic level, it serves as physical proof of tax compliance and regulatory adherence. In more advanced implementations, it forms part of a broader excise system supporting revenue protection, product authentication, and supply chain security.
Tax stamps are widely used by governments worldwide as a tool to support excise tax collection and anti-illicit trade measures. When combined with appropriate track & trace systems and enforcement mechanisms, they can help monitor the production, importation and distribution of taxed goods. Depending on the solution, production volumes and level of security required, the cost of a tax stamp typically ranges from a fraction of a cent to several cents per unit.
Types of Excise Marking Systems
In practice, excise marking systems and product identification solutions generally fall into two broad approaches:
- Direct marking (inline product marking systems): Direct marking is applied at high speed on production lines, using technologies such as inkjet printing, laser marking or ablation directly on the can, bottle or packaging surface.
Its main advantages include speed and seamless integration into industrial processes. However, its scope for advanced authentication and anti-counterfeiting features may be more limited, often relying primarily on inks, codes, and unique identifiers.
- Physical tax stamps (secure excise labels): Physical tax stamps are produced off-site on secure paper or polymer substrates and then affixed to the product or its packaging during the production process.
In some cases, they also function as closure seals, providing visible evidence if a container has been opened. They can be designed to be tamper-evident through appropriate material and adhesive choices.
Compared with direct marking, physical tax stamps provide a broader platform for security design and authentication technologies. They can incorporate multiple overt, covert and forensic features, while also enabling unique identification and integration with digital verification and track & trace systems.
4 Pillars to Protect Excise Revenues
Why Are Tax Stamps Alone Not Enough?
A tax stamp on its own is not sufficient to address illicit trade, counterfeiting, or tax evasion risks. Similarly, a unique identifier or a standalone database, when implemented in isolation, cannot fully mitigate the risks associated with diversion, counterfeiting or tax leakage.
Greater effectiveness is achieved when physical security features, digital identity, authentication technologies and traceability are combined within a coherent and integrated track & trace framework.
In practice, organizations sometimes approach the topic in a fragmented way, focusing on individual components such as tax stamps, serialization codes or compliance requirements, rather than considering how these elements work together within a holistic excise control system. However, effective excise control and illicit trade prevention require a more systemic approach.
A commonly adopted model is based on multiple complementary layers within a secure track & trace architecture:
- Layer 1: Tamper evidence and physical security (anti-counterfeiting protection)
- Layer 2: Serialization and supply chain visibility (product tracking and tracing)
- Layer 3: Authentication and revenue security mechanisms
When implemented together, these layers can help governments strengthen control over excisable goods, improve tax compliance, reduce fraud and illicit trade and gain better visibility across the supply chain visibility and transparency.
Authentication and Traceability: What Is the Difference?
Authentication and traceability are often discussed together in the context of excise control, anti-counterfeiting, and supply chain security. While closely related, they serve distinct but complementary functions within a secure track & trace system.
Understanding the difference between the two is essential for governments, regulators and industry stakeholders aiming to design effective solutions to combat illicit trade, protect tax revenues and improve supply chain visibility.
Authentication: Verifying What Is Genuine
Authentication addresses a fundamental question: Is this product, tax stamp, or identifier genuine?
It focuses on verifying whether a physical tax stamp, product, packaging element or digital code is authentic and has not been copied, altered or fraudulently reproduced. In excise systems, authentication is a key tool for inspectors, customs officers and other authorities tasked with identifying illicit, counterfeit or non-compliant goods.
Authentication can rely on multiple types of security features, often combined in layers:
- Overt features, visible to the human eye, designed for immediate recognition
- Covert features, which require simple tools such as UV light or magnification
- Forensic features, detectable only with specialized laboratory equipment
- Digital verification methods, including code-based verification using secure databases or mobile applications
The effectiveness of authentication depends not only on the security features themselves, but also on how they are used in the field, by whom, with which tools, and under what operational conditions.
Traceability: Tracking Movement Across the Supply Chain
Traceability addresses a different question within secure Track & Trace systems and supply chain traceability frameworks: where has this product been, and what has happened to it along the supply chain?
Traceability empowers stakeholders to track and trace a product’s journey from manufacturing to distribution, and, in more advanced systems, to trace it back from the market to its original source. This is accomplished primarily through serialization, which assigns a unique product identifier to each item, and by capturing supply chain events data at critical stages.
By linking these unique identifiers (UIDs) and recorded supply chain events, traceability provides comprehensive end-to-end visibility and transparency across the supply chain. This not only allows for effective monitoring of production volumes and distribution but also ensures quality and timely delivery. The resulting data strengthens accountability through documented transactions, supports audits and compliance, and enhances forecasting and operational planning with real-time information. Furthermore, traceability aids in promptly identifying and investigating issues such as misplaced products or discrepancies in shipment records, reinforcing supply chain integrity.
A robust track and trace system can capture and manage different types of data, such as:
- Production quantities and manufacturing data
- Lot or batch numbers for product grouping
- Expire dates
- Point of origin and manufacturing location
- Stock control information and inventory management data
- Shipment and dispatch events
- Aggregation relationships between packs, cartons and pallets
- Field-level events, including inspections and scans
The level of supply chain visibility achieved depends on how comprehensively the system is implemented and how consistently data is captured across the supply chain.
Complementary Functions in a Secure System
While product authentication and traceability serve different purposes, they are most effective when combined within a secure, integrated Track & Trace system.
Authentication helps determine whether a product is genuine at a specific point in time. Traceability provides the broader context, how that product has moved, whether its journey aligns with expected patterns, and whether any irregularities are present.
When combined within a well-designed system, these capabilities can significantly strengthen the ability of authorities to detect anomalies and suspicious supply chain patterns, support enforcement actions and reduce risks related to illicit trade, counterfeiting, tax leakage and supply chain abuse.
Rather than alternative approaches, authentication and traceability should be seen as complementary layers within a modern broader framework for secure excise management and supply chain control.
The Security Hierarchy: Different Users, Different Layers
One of the key principles in the design of tax stamps, secure authentication systems and anti-counterfeiting solutions is that security is not one-dimensional. An effective solution needs to address the requirements of different users, each with different levels of expertise, tools and operational contexts.
A commonly used way to structure this approach is through a multi-level security hierarchy, which can be described as follows:
- Overt features: These are visible, human-perceivable security features that can be recognized without tools by retailers or the public. Their purpose is immediate visual product identification, and they are typically designed to be eye-catching, distinctive and easy to recognize.
- Covert features for simple inspection: These features can be verified using simple tools such as magnifiers, UV lights or optical filters. They are typically used by retailers, customs officers or revenue inspectors for quick field-level authentication checks.
- Covert features for specialist inspection: These are designed for trained inspectors using more advanced equipment and verification methods. They provide an additional layer of multi-layer security protection beyond basic field verification.
- Forensic features: Forensic-level authentication features can only be detected and analyzed using specialized laboratory equipment. They are typically used in support of law enforcement investigations, legal proceedings or high-level verification.
The Authentication Triangle: Security Only Works If It Can Be Examined
An authentication feature does not operate in isolation within a secure Track & Trace ecosystem. Its effectiveness depends on the interaction between three key elements:
- The feature itself
- The examiner
- The required tool
This relationship is often described as an “authentication triangle”, a practical way to illustrate how authentication systems work in real-world conditions.
When designing a secure mark or tax stamp security feature, it is therefore not enough to consider only which feature to include. It is also important to address questions such as:
- How will the feature be examined in the field?
- Who will examine it (e.g., inspectors, customs officers, retailers)?
- What tools will be available for verification?
This perspective is essential for ensuring real-world effectiveness. A feature may be technically sophisticated, but if the intended user cannot locate it, understand it or verify it with the tools available in the field, its practical effectiveness may be limited.
Designing Effective Authentication Features
For authentication to be effective in operational environments, security features are typically designed to balance high-level protection, security and usability. Common characteristics include:
- Being difficult to copy, imitate or reverse engineered (enhancing anti-counterfeiting resilience)
- Being accessible and recognizable for the intended examiner (supporting field authentication)
- Being integrated into the document or tax stamp design
- Being resistant to removal without damage (supporting tamper-evident security)
- Being difficult to alter (protecting product integrity)
- Being cost-effective in relation to the risks addressed
In practice, the design of tax stamps and secure marks combines multiple elements, such as printed graphics, specialized security inks, varnishes, substrates, adhesives and digital authentication markers, into a layered authentication architecture.
Each Layer as a Canvas for Authentication
A secure tax stamp is more than a printed label. In practice, multiple elements of the stamp can be designed to contribute to its overall security.
These may include:
- Printed graphics (including complex guilloches and secure design patterns)
- Micro optic security features (micro‑lens and motion‑based optical elements), optical security features based on micro‑lens arrays or micro‑structured elements that create dynamic visual effects (motion, depth, image switching) when viewed at different angles
- Specialized inks (UV, IR, optically variable inks)
- Varnishes and coatings
- Microtext and fine-line structures (for covert authentication)
- See-through registers
- Specialty substrates (paper, polymer, polycarbonate)
- Tamper-evident materials and security adhesives
- Unique identifiers (UIDs for serialization and traceability)
- Digitally readable codes (QR codes, Data Matrix, barcodes for Track & Trace systems)
In addition, authentication can be supported by external tools and systems, such as mobile-enabled verification mechanisms and secure verification databases.
The choice of substrate also plays an important role in overall tax stamp security design. Materials such as paper, polymer, polycarbonate or frangible substrates can contribute to tamper evidence and resistance to removal or reuse. The physical and visual design of the stamp is therefore a key consideration: security features are generally more effective when they are fully integrated into the document, rather than appearing as isolated or add-on elements.
The objective of this layered security and authentication approach is not to make copying impossible. Given the continual advancements in technology and the ingenuity of counterfeiters, it is unrealistic to expect complete prevention. Rather, the goal is to make imitation sufficiently difficult so that a trained examiner can reliably distinguish genuine items from counterfeit or illicit goods, strengthening excise enforcement, brand protection, and global supply chain integrity.
From Serialization to Secure Track & Trace
At the digital level, modern excise control systems and digital track & trace solutions are typically based on unique identifiers.
Serialization assigns a UID – a unique identifier – to each unit, enabling products to be individually identified and, where systems are fully implemented, tracked and monitored throughout the supply chain. These identifiers may be encoded in 1D barcodes, QR codes, Data Matrix code symbols or proprietary digital formats, depending on the use case and system design.
Once serialization is in place, the next step is to connect product identity to supply chain events, which include production, verification and authentication checks, aggregation, dispatch and shipping events, receipt, warehousing processes, first retail, and field inspection. These events collectively ensure that each product can be tracked and its journey documented throughout the supply chain, providing a comprehensive traceability framework.
A secure track & trace system also needs to address practical key implementation questions, including:
- Where and how will unique identifiers be generated and issued?
- Who will read, scan and verify them, and with which devices?
- How will the data be stored, secured and accessed across systems?
- How will anomalies be identified and analyzed?
- How will data be used to support enforcement actions and risk management?
More advanced track and trace systems go beyond product marking. By combining identification, event data and analytics, they can support accountability, improve forecasting, detect unusual patterns in the field and strengthen compliance monitoring across the excise value chain.
Why This Matters for Governments
For governments, the value of tax stamps, authentication systems, and traceability programs extends beyond regulatory compliance.
When properly designed and implemented, these systems can:
- Contribute to increasing excise and tax revenues
- Improve monitoring of legal production, distribution and imports
- Help detect diversion and suspicious supply chain events
- Support treaty and regulatory compliance
- Strengthen enforcement capabilities
- Reduce reliance on manual, paper-based processes and self-declaration
- Improve visibility across manufacturers, distributors and retailers
- Enable data-driven decision-making and risk-based audits
In markets affected by illicit trade and counterfeit goods, traditional control mechanisms, such as physical counts, on-site inspections and paper-based records, may not always provide a complete or reliable picture. Without secure product identifiers, event monitoring, authentication tools and robust data analysis, gaps in oversight can persist.
This is particularly relevant in sectors such as tobacco, pharmaceuticals, and alcohol, where illicit trade is associated not only with lost tax revenues but also with broader public health risks and safety concerns. Lower-priced illicit products may increase consumption, undermine tax policies and expose consumers to goods that fall outside regulatory controls.
For these reasons, tax stamps and track & trace systems are increasingly viewed not simply as compliance tools, but as part of a broader digital transformation of excise management—one that connects tax collection, enforcement, public health, compliance and governance.
The Role of Regulation: Technology and Legislation Must Evolve Together
One recurring issue in this field is the gap between regulation and practical implementation (technology deployment).
The Protocol to Eliminate Illicit Trade in Tobacco Products under the WHO Framework Convention on Tobacco Control (FCTC) has made Track & Trace systems and supply chain monitoring a central element of tobacco control policy. However, its practical implementation continues to leave room for interpretation. Article 8 has led to different interpretations regarding what should be considered “secure,” as well as how data sharing, governance structures and system independence should be defined.
This complexity can create challenges for governments. It also highlights why legislation should not be treated as a separate step from solution design. In practice, programs tend to be more effective when legal, tax, operational and technical governance considerations are addressed in an integrated way from the outset.
Governments therefore need to understand not only the available technologies, but also a broader set of strategic and operational questions, including:
- What governance model should be adopted for Track & Trace systems
- Who should issue and manage unique identifiers (UIDs)
- How to ensure appropriate system of independence from industry influence
- How to structure procurement models
- How enforcement will be organized and supported
- How data will be shared securely across agencies and stakeholders
- How national systems will align with international standards and treaty obligations
In this context, excise modernization and Track & Trace implementation is not solely a technological decision. It is a broader policy, enforcement and system-design challenge.
Common Misconceptions Still Holding the Market Back
Despite increasing attention to excise control systems and illicit trade prevention, the development and adoption of secure Track & Trace systems are still influenced by several persistent misconceptions. These assumptions can shape policy decisions, procurement approaches and excise system design in ways that limit overall effectiveness and long-term revenue protection.
Some of the most common include:
- “Track & Trace solves illicit trade completely”: No single Track & Trace system can eliminate illicit trade on its own. However, well-designed Track & Trace systems can play a critical role in improving supply chain visibility, supporting enforcement actions and strengthening overall compliance. Their effectiveness depends on how they are integrated with broader regulatory, operational and excise management frameworks.
- “It is too expensive”: Cost is often perceived as a barrier, but this view may overlook the broader return on investment (ROI) of secure excise systems. When tax leakage, diversion and weak control mechanisms are considered, secure systems can deliver significant long-term value. The overall impact depends on the quality of implementation, governance and enforcement.
- “The technology is not ready”: Many of the core components of Track & Trace technology, such as serialization, aggregation, secure identifiers (UIDs), mobile authentication and event monitoring, are already well established. These technologies have been successfully deployed at scale in highly regulated sectors, including pharmaceuticals track and trace and other controlled industries.
- “Increased taxation alone addresses illicit trade”: While taxation is an important policy lever, it is not sufficient on its own. Without effective supply chain monitoring, enforcement and control mechanisms, illicit markets can continue to operate alongside legal supply chains, reducing the impact of fiscal measures.
- “Basic functionality is enough”: Systems designed solely to meet minimum compliance requirements may not fully address the complexity of illicit trade networks and global supply chain risks. More comprehensive approaches typically combine physical security, digital traceability, multi-layer authentication, data analytics and enforcement support to deliver more robust and sustainable outcomes.
Moving Beyond Misconceptions
Addressing these misconceptions is an important step toward more effective excise control modernization. As governments and industry stakeholders continue to evolve their approaches, there is growing recognition that secure Track & Trace systems are not standalone tools, but part of a broader framework that combines technology, governance and enforcement.
Essential Elements of a Robust Excise Solution
A mature tax stamp system and secure track & trace program is typically built on a combination of technical, operational and governance principles. At its core, an effective exercise control system needs to be secure and robust, but also scalable, interoperable and designed to function in real-world conditions. It should support the needs of different stakeholders across the value chain, ensure an appropriate level of independence from industry actors and be closely integrated with law enforcement activities and regulatory authorities. Equally important is the ability to manage and analyze data effectively, enabling informed decision-making and risk-based oversight.
Beyond these foundational principles, robust excise systems rely on a set of interconnected operational components. Security features, ranging from overt and semi-covert elements to covert, forensic and tamper-evident technologies, play a central role in protecting the integrity of tax stamps and enabling field-level authentication. At the same time, supply chain event monitoring allows authorities to track product movements and detect irregularities, while fraud detection and investigation capabilities support enforcement actions.
These systems are underpinned by secure digital infrastructure, including protected databases and network connections and data governance frameworks, as well as accounting and audit mechanisms that ensure consistency between issued, distributed and applied tax stamps. Physical security controls are also critical, particularly in the production, storage and transport of stamps and related materials, alongside controls over wastage and destruction processes.
Finally, the role of trusted suppliers should not be overlooked. Certified or otherwise qualified security printing capabilities, together with reliable technology partners, contribute to the overall integrity and resilience of the system.
When these elements are not considered in an integrated way, excise programs may become fragmented, less resilient or overly focused on cost rather than effectiveness. By contrast, a well-designed integrated excise solution combines these components into a coherent framework that supports revenue protection, regulatory compliance and long-term sustainability.
Why Education Is Becoming a Strategic Differentiator
One of the emerging themes in the evolution of excise control systems and Track & Trace implementations is the growing importance of education and capacity building, not only at an operational level, but also at a strategic and institutional level.
Discussions in industry forums, round tables and international working groups suggest that stakeholders continue to seek greater clarity on key topics such as global standards, governance responsibilities, interpretation of the FCTC Protocol, Track & Trace system architecture and cross-agency data sharing. In some markets, there is also an ongoing need to further develop capabilities in areas such as data analytics for audit, legislative design and end-to-end excise system management.
In this context, solution providers can play a broader role beyond technology delivery. Companies with experience in regulated industries can support governments and stakeholders through:
- Technical content and knowledge sharing
- Training and institutional capacity building
- Interpretation of regulations and international standards
- Implementation guidance for Track & Trace systems
- Dissemination of best practices
- Support for secure, interoperable and independent system architecture
For a company such as Antares Vision Group, this represents a natural extension of its experience. While relatively newer in some excise segments compared to its established presence in pharmaceuticals, the Group brings expertise in serialization, traceability, regulatory compliance and secure supply chain design developed in a highly regulated environment.
Combined with Crane Authentication’s capabilities in physical and digital authentication, this creates a complementary offer that can support not only technology deployment, but also a broader understanding of how to design and implement effective systems.
This reflects a wider shift in the market, where the focus is gradually moving from individual components toward integrated excise solutions, and from product supply toward more comprehensive support in system design, implementation and long-term optimization.
Toward Integrated and Secure Excise Systems
Tax stamps, authentication technologies, and Track & Trace systems are increasingly seen not as stand-alone fiscal labels, but as part of a broader security and intelligence infrastructure designed to protect revenues, strengthen enforcement, support public policy and reduce illicit trade.
Authentication and traceability are not competing concepts. They represent complementary layers within a unified Track & Trace architecture. Authentication helps verify whether a product or mark is genuine, while traceability provides visibility into where that product has been, what has happened to it and whether those events align with legal and fiscal expectations.
For governments, these systems can deliver a range of benefits, including improved revenue collection, stronger compliance, enhanced visibility and more effective enforcement. In regulated sectors involving human consumables, secure excise systems can also support public health and consumer protection objectives.
The challenge is not only technological. It is also educational, legislative and organizational. In many markets, there is still a need to further develop understanding of what constitutes a “secure” system, how governance should be structured and why end-to-end design is critical.
There is a growing shift toward solution models that combine physical security, integrated tax stamp systems, digital traceability, authentication technologies, data analytics and institutional support. In this context, the ability to integrate technical expertise, regulatory understanding and practical implementation experience is likely to become an increasingly important differentiator in the evolution of secure excise systems.
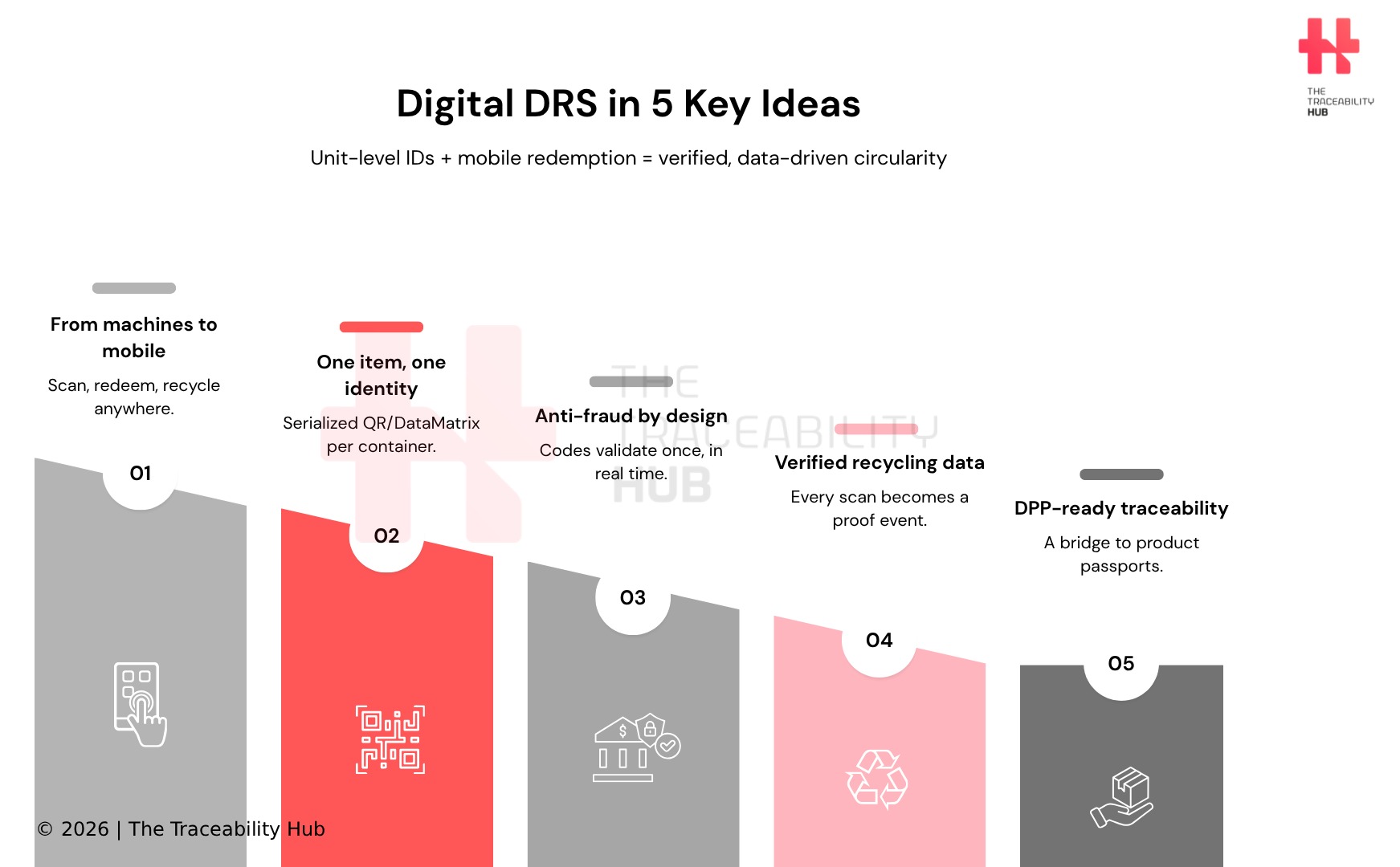
Read more: Digital DRS: The Next Frontier of Packaging Traceability and Circularity






